ESCAR 2017
This week, I attended ESCAR Embedded Security in Cars
conference in Ypsilanti, Michigan. As my first conference I attended, I learned
the valuable lessons: insight to fields and areas I have not been introduced
before and potential to network with people in industry and academia. One very
interesting presentation was use of ChipWhisperer to perform side-channel
attacks to crack passwords and encryption using differential power analysis on
common processors such as STM32F2.
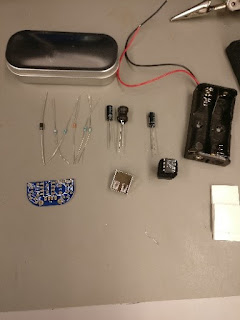
During breaks, I attended multiple vendor booths and one in
particular caught my attention. It was GRIMM. GRIMM engineers were able to have
almost full access to one of the Ford Focus’s CAN bus without proprietary
information. One thing that stood was how easy it is to get an access to the
bus. In fact, they had a couple of demos where we could learn how to read
packets to narrow down a function. They
gathered all the items from a single car from a junkyard. It is almost scary to
know how easy it is to crack a car and control its power locks, warning lights,
and instrument cluster.


Comments
Post a Comment